Why IoT and edge matter for federal
Every federal mission that leaves the data center touches embedded systems. Border sensors for DHS, perimeter cameras at DoD installations, seismic sensors at USGS, weather stations at NOAA, water-quality buoys at EPA, air-traffic sensors at FAA, and the entire tactical edge for the armed services. The Department of Defense calls the environment DDIL — Denied, Degraded, Intermittent, Limited — and that phrase is load-bearing. If your system assumes a warm connection to a cloud region, your system does not work at the edge.
Precision Federal builds IoT and embedded systems designed for that reality. We are a SAM.gov registered small business (UEI Y2JVCZXT9HP5, CAGE 1AYQ0, NAICS 541512) with the engineering depth to own the device, the telemetry pipeline, and the cloud fleet manager — not stitch three vendors together.
FEDERAL IOT DEPLOYMENT
What we deliver
Embedded Linux
Yocto, Buildroot, or Ubuntu Core. Reproducible images. dm-verity root, A/B partitions for safe OTA, secure boot chained to TPM or Jetson Security Engine.
Edge inference
PyTorch to TensorRT / ONNX Runtime on Jetson; Core ML on Apple Silicon for certain deployments; TFLite on microcontrollers where we can't escape one.
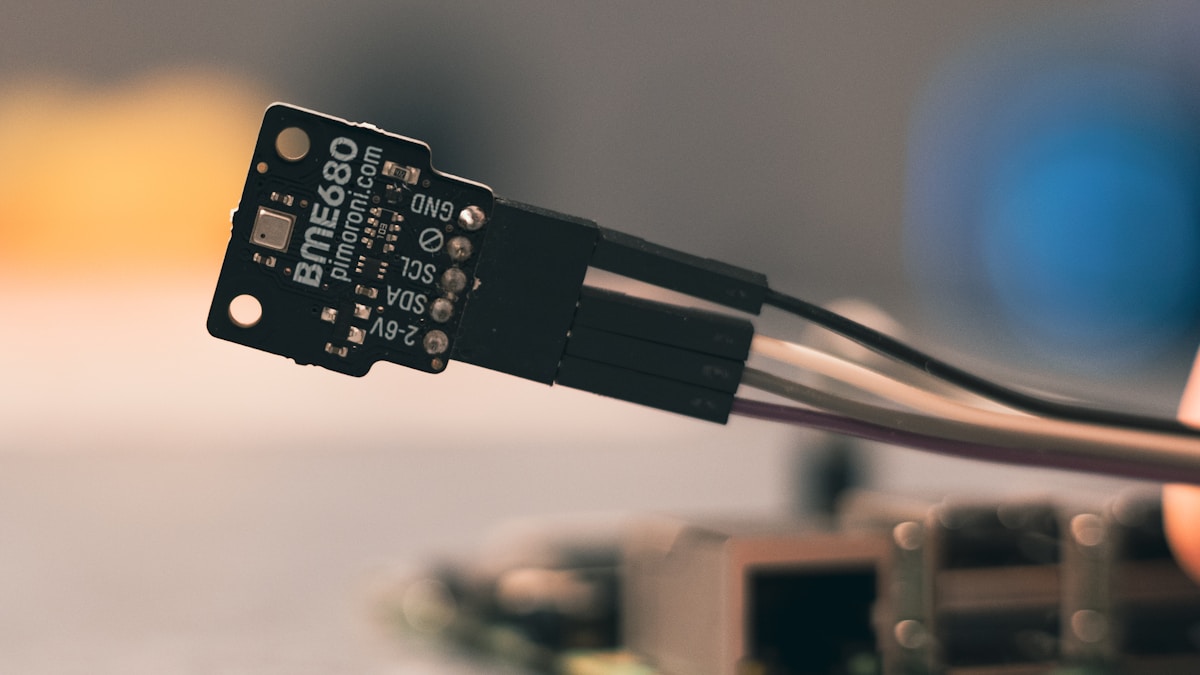
Sensor integration
I2C, SPI, UART, CAN, Modbus, GPIO, MIPI CSI-2. Thermal, RGB, IR, LiDAR, radar, acoustic, and chemical sensors.
Fleet management
AWS IoT Core + Greengrass, Azure IoT Hub + IoT Edge, or a self-hosted MQTT + Mosquitto fleet with a custom orchestrator when the program's risk profile requires sovereign control.
Telemetry pipelines
MQTT → Kinesis/Kafka → time-series store (Timestream, InfluxDB, TimescaleDB) → dashboards. With backpressure, batching, and lossless replay.
OTA & model updates
signed bundles, staged rollouts, canary cohorts, automatic rollback on health regression.
Field dashboards & mobile companions
508-compliant React dashboards and React Native apps for technicians in the field.
Target hardware
We optimize for a small, well-supported set of platforms. Selecting outside this list is an active decision — not a default — because the cost of obscure hardware is measured in years of maintenance, not weeks.
NVIDIA Jetson Orin
Nano (8 GB) for vision inference under ~15 W, NX for mid-tier, AGX for compute-heavy multi-stream workloads. First-class CUDA, TensorRT, and DeepStream support.
Raspberry Pi Compute Module 4 / 5
~$75 nodes for low-power sensor fusion and MQTT publish. Commercial temperature range limits outdoor use without enclosure engineering.
NXP i.MX 8M Plus
industrial Linux with NPU for vision inference up to ~2.3 TOPS. Long supply availability, native CAN and TSN.
Qualcomm RB5 / RB6
rugged robotics-oriented platform with 5G modems and higher NPU throughput.
Rugged defense boards
Curtiss-Wright, Mercury, Abaco VPX when the program requires MIL-STD-810 and VITA 46 form factors.
Microcontrollers
ESP32, Nordic nRF52/91, STM32 for battery-powered telemetry nodes. MicroPython for rapid prototyping, C for shipping.
Reference architectures
1. Installation perimeter sensor fleet
Hundreds of Jetson Nano nodes with RGB + thermal cameras running a detection model at 15 FPS. Each node publishes detections to a regional MQTT broker over TLS 1.3 with certificate authentication backed by the installation's PKI. Broker federates up to AWS GovCloud IoT Core. Fleet manager tracks device health (CPU, GPU, disk, temperature), model version, and last-seen timestamp. OTA model updates staged in cohorts of 10 %, 25 %, 100 %.
2. Tactical DDIL vehicle-mounted inference
AGX Orin mounted in a vehicle, fused inputs from IR camera and LiDAR. On-board inference generates entity tracks that are both displayed locally on a hardened tablet and queued for exfiltration when a link is available. CRDTs keep local and reach-back state eventually consistent. No dependency on cloud liveness — the mission continues regardless.
3. Environmental monitoring network
Solar-powered ESP32 nodes publishing temperature, humidity, wind, and air-quality readings over LoRaWAN to a regional gateway. Gateway aggregates and forwards to a cloud time-series store. Dashboards render 30-day rolling windows; anomaly detection runs nightly and flags sensor drift or hardware failure before it shows up in the data product.
4. Body-worn and wearable telemetry
Bluetooth LE wearables pairing with a phone running a React Native companion app. Device firmware in C on Nordic nRF52. Phone provides the uplink via agency MDM-managed cellular. Data flows into a FedRAMP-moderate cloud tenant with per-user segregation. Privacy by design — minimum necessary data, on-device aggregation, no raw location unless the contract explicitly requires it.
Security and supply chain
We design with the assumption that devices will be physically recovered by adversaries. That changes everything. Concrete controls:
- Secure boot rooted in TPM or vendor secure element. No unsigned kernels, no unsigned initramfs.
- Full-disk encryption on all non-read-only partitions. Keys sealed to TPM PCRs.
- Per-device provisioning with unique X.509 certificates issued from a managed private CA.
- Zero static credentials in firmware. No hardcoded Wi-Fi passwords, no embedded API keys.
- Remote attestation before key release or high-value telemetry. If the boot chain or firmware hash doesn't match, the device refuses to enable its operational material.
- CycloneDX SBOM generated for every image. CVE monitoring tied to fleet management so known-vulnerable devices get prioritized for patching.
- Tamper-evident enclosure options and secure zeroization on intrusion detection for the highest-risk deployments.
Federal use cases we target
We focus on programs where small-team ownership of device-plus-cloud-plus-UI delivers more than prime-subcontractor chains. See our DoD page, DHS page, and Army page for program-level detail. Related insights: tactical edge ML brief and Jetson federal deployment guide. Historical parallels in sensor fleet modernization.
What we do not do
We do not design custom silicon. We do not fabricate boards. We do not build MIL-STD enclosures in-house — for those we partner. We are a software-and-integration shop that is fluent enough in hardware to pick the right platform, talk competently to board vendors, and debug SPI and CAN with a logic analyzer when we need to.